- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
I’ll start by stating the obvious: you are in business to make money. It might have started out as a hobby-turned-lifestyle-business, but that’s not sustainable in the long-term. So you took a business course or two, went to a couple of conferences, talked with your friends in the field, and bought some back-office software. Now you’re paying for a bunch of services that all do different things, you’ve got scripts and automations to tie them all together, you pray the internet doesn’t go down, and you’re watching your profits diminish. What version of hell is this?
This is that period of time where your business has grown organically and you need to gather it all up and streamline functions. The tools in your stack are running you, rather than behaving as your tools. To get back your profits you need to look at your TCO, your Total Cost of Ownership.
What is TCO?
It’s just math, and simple math at that. Total Cost of Ownership has a simple formula:
Purchase Price + Costs of Operations = TCO
Nobody ever calculates the cost of a pet or a child because if you had to decide based on what the 20 year TCO would be, nobody would ever have kids or pets. Also, it’s impossible to quantify unconditional love, compassion, and the multitude of other feels you get from either pets or kids. I mean, really, how much is a peanut-butter-and-jelly-faced kiss worth these days?
The shorter the ownership term, the more accurate the TCO.
Today we’ll talk about what TCO is in relation to your IT Stack and how lowering it is a GoodThing™.
The IT Stack
Your stack consists of the entire alphabet of tools you use to manage your users. That includes, but is not limited to, your:
- PSA (Professional Services Automation): ticketing, project management, time tracking, invoicing
- RMM (Remote Monitoring & Management): patch management, content distribution, app updates
- MDM (Mobile Device Management): manages and secures your mobile devices
- IDM (Identity Management): create and manage user identities across your portfolio
Each of these services cost money. Some of them have similar features and all of them need to be configured and managed separately.
The cost of your stack is more than simply the monthly costs for each service. You also have to take into account the cost of the employee(s) configuring and managing the service, the cost of support from the vendor, the computers you’ll use to manage the services, the time it takes to initially configure the product, the time it takes to configure automations between the products. You also need to include the cost of training your employees to use the services and to stay up to date. Some of these products have conferences, which should also be included in the TCO figure.
Don’t Forget These Costs
As if those weren’t enough considerations, you also have to consider the amount of time it takes to onboard your users, which should include: communicating the change to a new system, setting up the appointment to distribute the new service, the time spent installing the new service, and the post-install support.
You may have to engage your accountant or accounting department to be sure your PSA’s billing system is done correctly, so that the information coming from it gives expected results to your accounting software. All of your fields need to map to shared apps properly. Will your current staff be able to handle all of these tasks or will you need to hire an employee or contractor to set this up? Our Zero Trust whitepaper states:
“The SaaS market tends to encourage companies to keep up with the latest and greatest tech; companies, in turn, end up stacking their infrastructure with security tools that lack cohesion and strategy. This ad-hoc purchasing approach and high tool volume tend to move companies further away from Zero Trust rather than closer to it.
These cluttered infrastructures require many complex integrations to get tools to work with one another. They likely contain many dependencies (which are likely not all documented) that slow any agility that the tools might have promised. Anything from a tool update to a new addition to the stack can break one integration, sending a domino effect through the rest of the infrastructure.
Businesses working within such an environment, therefore, hesitate to make sweeping changes to adopt Zero Trust. Businesses that went this piecemeal route to achieve Zero Trust might have abandoned the cause after witnessing an ever-increasing complexity without any increased security to show for it.”
Ways to Reduce TCO
All of the above need to be included in your estimation of the cost of your stack. If it sounds like a daunting task, that’s not surprising. It’s a lot. How do you ease the financial strain of your IT stack while maintaining the integrity of your IT service?
Consolidation
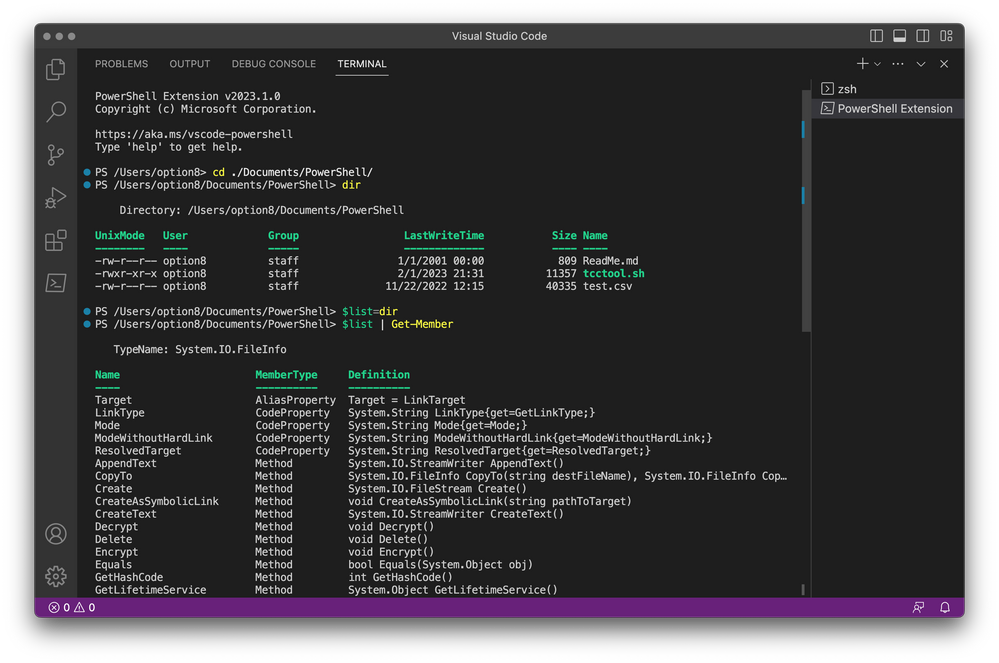
Grab your favorite spreadsheet tool and prepare to create a matrix. Consolidation is your friend. List out your tools in column A and on Row 1 input the features you use in each of your tools. Then match up which tools have similar enough offerings that you can consolidate them. We know you can do this. Everyone has extraneous apps they pay for because they’re used to the product, rather than because said product provides real value.
When it’s time to actually move your users to the new product, use the new tool to remove the old tool. This reduces or eliminates downtime for your users.
Adopt a Zero Trust Strategy
When you start developing a strategy that secure identities rather than passwords, you give your customers the ability to have true SSO with all of their cloud apps. And when you add MFA, MDM, conditional access policies, and patch management to the mix you have the ability to pare down your individual tools. When you pare down your need for multiple tools, you reduce your TCO. When you reduce TCO, you increase profits.
Other Options for Reducing Your Stack’s TCO
Rather than using on-prem tools and incurring their high ongoing support costs, you could move your support stack to the cloud. For a single monthly fee that is typically lower than supporting a variety of on-prem hardware and software, you can get all the functionality you and your users need. And when Zero Trust is part of that picture, you have a secure functioning stack at a price that doesn’t destroy your budget.
If you’re already using cloud-based systems, you should consider automating your stack as much as possible. Your PSA should have automation tools that will route tickets, send up automatic warnings and responses, or fire off actions in your RMM or MDM. You should be scheduling patches in your MDM and using policies to manage authorizations. Insights helps you discover which automations need to be created to prevent Shadow IT. Your “hands-on” time with customers or users should be for solving problems rather than for performing updates and upgrades.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.