- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Security is always on MSPs’ minds, it’s one of the most important services that they offer to their clients. Datto research tells us that a massive 99% of MSPs already offer security services to their clients. This is, of course, no surprise.
Having been in the MSP community a long time and having discussed it a lot I believe that MSPs agree that multi-factor authentication (MFA) is a key tool that can help protect the clients they support. And it’s not just me:
- The US Cybersecurity & Infrastructure Security Agency is very clear about this for all businesses: “Always Enable MFA”.
- HIPAA has an MFA requirement and Kaseya partners who were polled as part of their 2022 MSP Benchmark Survey show HIPPA as the top compliance challenge for their partners.
- In the UK, the National Cyber Security Centre lists MFA as a key part of its Cyber Essentials framework. The Australian Cyber Security Centre states – as part of their Essential Eight program – states that “Multi-factor authentication is one of the most effective controls an organization can implement to prevent an adversary from gaining access to a device or network and accessing sensitive information”
- Finally, according to Microsoft, MFA can prevent 99.9% of attacks from succeeding. And yet, despite this, it still isn’t being adopted widely.
This all seems pretty clear… right?
However, according to research from N-able, only 30% of their MSPs’ end-user clients are using MFA for all of their applications. They expect this to increase to 95% by 2026, but what is causing the delay?
68% of Datto partners currently offer MFA solutions to their clients, but the takeup on these will be considerably lower and even if 68% are using these solutions it leaves a large number that aren’t.
UK based Web Security firm Portswigger’s research shows that only 39% of SMEs are using MFA and that 55% of SMEs are not even aware of it.
Even in our personal lives it’s the same. Twitter reported that in 2021 only 2.5% of users have applied MFA to their accounts. Have you? It’s simple to do, so if not, why not?
Why isn’t the adoption higher?
I’ve given this some thought and below are a list of common reasons I hear from MSPs when I ask about MFA adoption:
- It’s too hard, too inconvenient, and adds too much friction. This is the old faithful response – it’s too hard. I’m sure people said the same when keys were introduced to doors. Security is always a balancing act between convenience and protection, but the benefit really outweighs any inconvenience and MSPs should be able to explain this to their clients.
- We use a password manager. This is great! password managers really help and having secure and unique passwords for all of your applications and services will reduce your chances of being compromised. The two aren’t mutually exclusive: Password Manager + MFA together are a great solution for both your MSP internally and for your clients.
- We share admin accounts. This applies more to MSPs than to their end user clients, but this is no barrier now. Ensure you deploy an MFA solution that allows the secure sharing of your MFA tokens so that all of your staff can securely access the applications they need.
- Our clients won’t adopt it. MSPs are often afraid to force clients to use MFA, fearing it could damage – or even end – their relationship. We need to consider what MSPs are, though. We talk about being Trusted Advisors a lot and this is an actionable example of explaining to clients how the benefits of enabling MFA outweigh the minor inconveniences.
- It’s too expensive. This may have been an issue once, but it isn’t anymore so should be a very easy objection to overcome.
- Our software doesn’t use it. Well, this should be setting off alarm bells! If not, why not? Maybe it’s time to change the software you are using.
- Staff won’t install an authenticator on their personal phone. I’ve heard this excuse a few times. While it is a valid argument, if the staff member can’t be convinced to install a small app and the client won’t provide phones, then hardware tokens can (and should) be used in its place.
What can we all do?
MSPs have a lot to do in order to achieve 95% adoption by 2026. They will have to really increase the speed of adoption. I think the following can help:
Education
Perhaps the single most important thing MSPs can do is educate their clients. Explain the risks of NOT using MFA, explain the risks of reusing passwords across applications, and explain that – contrary to popular belief – SMEs are targets for cyber criminals.
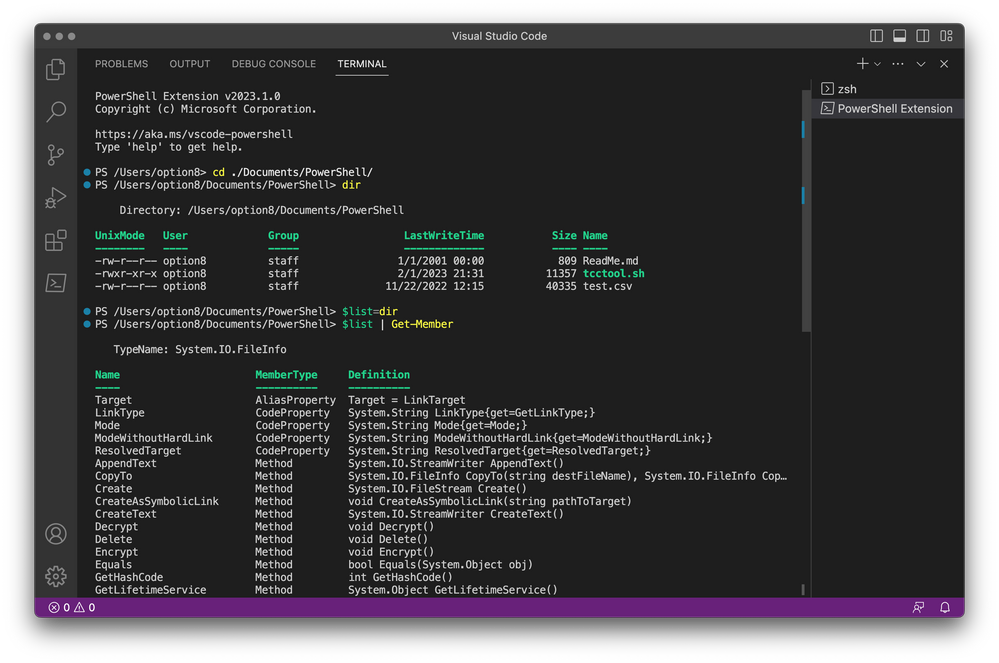
Use an MSP-Friendly MFA Solution
Your clients look to you for security, so it’s important that you can deploy and manage their MFA solutions for them. Having a solution that can be managed via a simple multi-tenant portal is vital and having integrations with leading PSA solutions will streamline the MSP’s Service Desk to resolve any issues that arise.
Get Moving
As the old Chinese Proverb says “The best time to plant a tree was 20 years ago. The second best time is now.” It’s the same with MFA: ideally it should have been done earlier, but the best time to create an action plan to ensure all of your clients are protected is now.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.