Hardening Windows Devices with CIS Benchmarks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-28-2022 12:48 PM
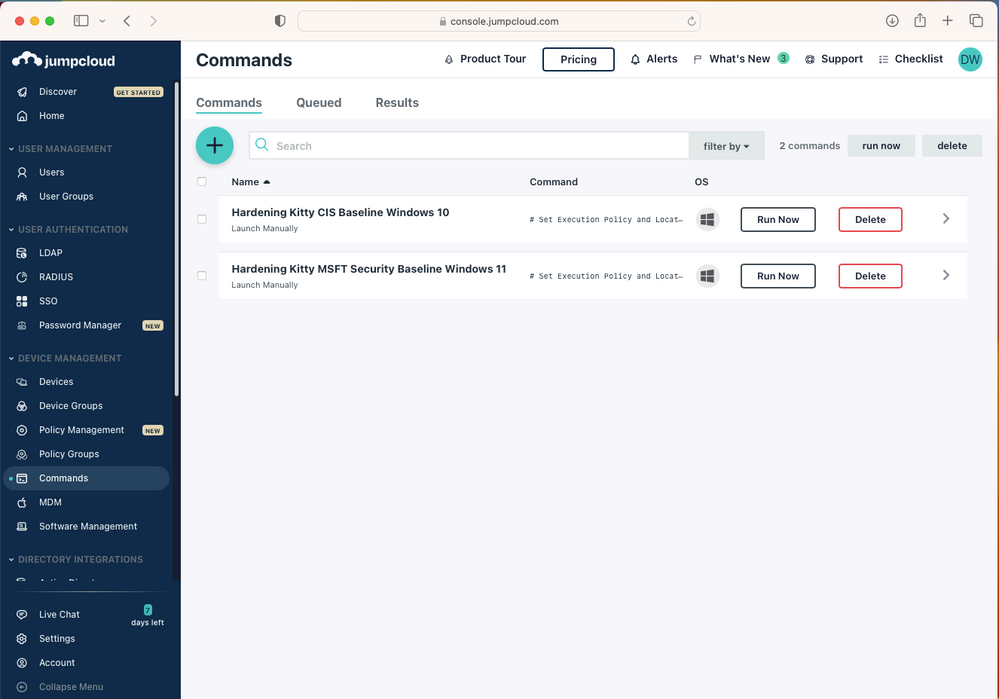
My colleague Juergen published a guide to hardening Windows using CIS (or Microsoft benchmarks) through JumpCloud's Commands. It was extremely easy to do in three steps:
1) Download the benchmark (CSV) and PS Script from the Hardening Kitty repository on Git.
2) Create your policy in JumpCloud, along with a script, and upload the two files.
3) Run it either manually or on a schedule against a / multiple device groups - once you added a device to the group, it will get the cmd run in the next schedule.
- Labels:
-
Security & Zero-Trust
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2023 03:10 AM
Hi @JCDavid
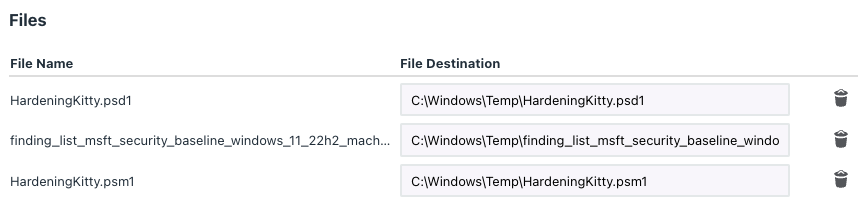
Update on this - since HardeningKitty 0.9.0 is now a Powershell-Module.
The command has to look like this:
Import-Module C:\Windows\Temp\HardeningKitty.psm1
Invoke-HardeningKitty -FileFindingList C:\Windows\temp\finding_list_msft_security_baseline_windows_11_22h2_machine.csv -Mode Audit -Report
- Download the module from their Github
- attach the files to the Command
- Import the Module
- Invoke whatever action is desired (in this example it's only Audit-Mode with a Report for the MSFT baseline)