Disclaimer
JUMPCLOUD EXPRESSLY DISCLAIMS ALL REPRESENTATIONS, WARRANTIES, CONDITIONS, AND LIABILITIES OF ANY KIND ARISING FROM OR RELATED TO THIRD-PARTY SOFTWARE, SCRIPTS, REPOSITORIES, AND APIS. JUMPCLOUD IS NOT REQUIRED TO SUPPORT ANY SUCH THIRD-PARTY MATERIALS AND ALL RISKS RELATED TO THIRD-PARTY MATERIALS ARE YOUR RESPONSIBILITY. PLEASE ALSO REVIEW THE JUMPCLOUD TOS.
Deploy GTB Endpoint Protector Agent via JumpCloud
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-02-2025 08:49 AM

To install GTB Endpoint Protector on your Mac devices using JumpCloud, there are 5 steps:
- Download the Endpoint Agent.
- Generate and deploy the TCP Protector Certificates.
- Modify and deploy a preconfigured configuration profile to grant Full Disk Access, allow System Extensions and deploy certificates via JumpCloud MDM.
- Deploy the GTB Endpoint Agent via JumpCloud Private Repo.
- Configure the GTB Endpoint Agent via JumpCloud Commands.
Download the Endpoint Agent:
First, we begin by downloading the GTB Endpoint Agent installer DMG file.
- Sign in as Administrator to the GTB Central Console from the browser.
Navigate to Downloads > macOS Endpoint Agent and download the Endpoint macOS Agent + Networking DMG file on the local drive.
- Mount the DMG file, drag and drop the PKG installer file from the DMG to the Desktop. We’ll use this PKG installer to deploy the Agent later.
Generate and deploy the TCP Protector Certificates:
Generating Certificates:
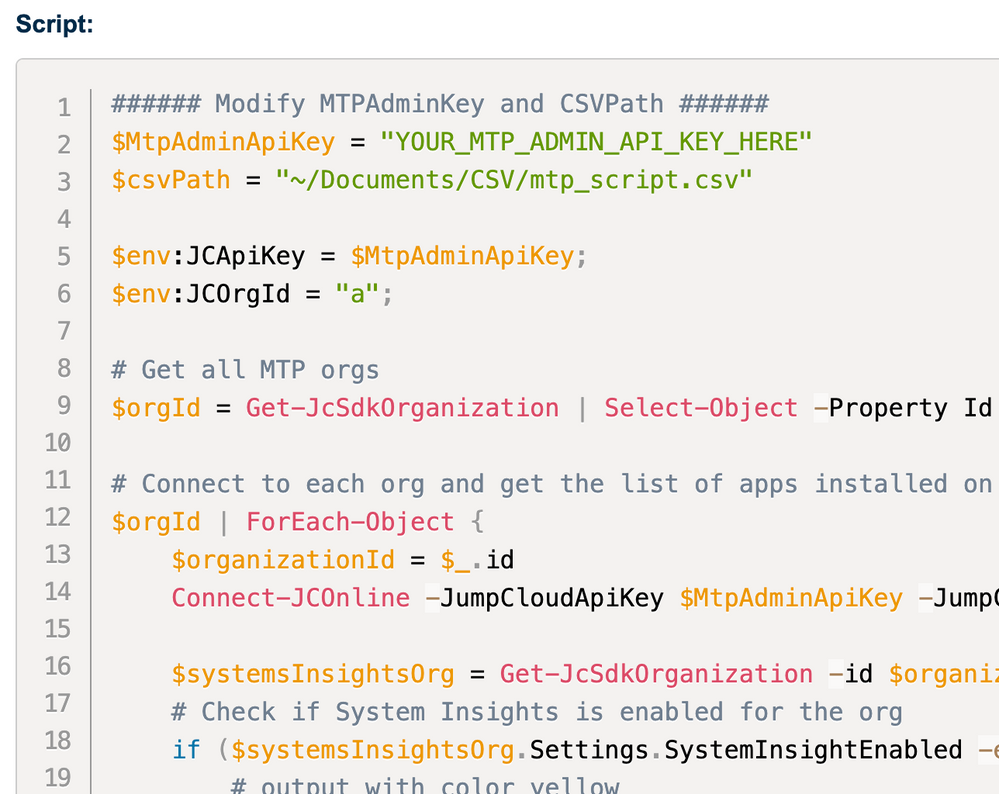
- Download the script to generate the certificate.
- Open the downloaded script file in any text editor or code editor like Visual Studio Code or Sublime Text.
- For the "_cert_dir" variable, enter the local path where the certificate will be saved and save the script. Since this step is to be done on the admin’s device, you can choose any path like "/Users/$USER/Downloads" to generate the certificates in the Downloads folder.
- Next, we open the Terminal, navigate to the folder where the script file is located and execute the below commands:
chmod +x cert-utils.sh ./cert-utils.sh -g
- The script would generate two files - "tcp-protector-ca.der" and "tcp-protector-ca.pem" in the Downloads folder.
- You need to upload both the files to a public cloud repo like AWS S3 Bucket or Azure Blob etc. or a web server from where they can be downloaded publicly. (Google Drive, OneDrive, Box storage etc will not work.)
- These certificates come with a validity of 1 year from the date of generation.
Deploying the Certificates via JumpCloud Commands:
- In JumpCloud Admin Console, navigate to Commands and set up a new Command.
- Configure the below script for Mac device(s), set to run as 'root' and Time Out set to '200' seconds:
mkdir /var/tmp/.cert.tmp cd /var/tmp/.cert.tmp curl -O NETWORK_PATH_TO/tcp-protector-ca.der curl -O NETWORK_PATH_TO/tcp-protector-ca.pem
- Replace "NETWORK_PATH_TO" with the public URL of AWS S3 or Azure Blod where the certificates are uploaded.
- Assign to the target Mac device(s) and execute the Command. This step will make a ".cert.tmp" folder inside the "/var/tmp" directory and download the certificates from the public repo to this folder for GTB to use.
Modify and deploy the preconfigured configuration profile to grant Full Disk Access, allow System Extensions and deploy Certificates via JumpCloud MDM:
- First, download the preconfigured MDM configuration profile provided by GTB from here.
- Open the downloaded configuration profile using any profile editor like iMazing Profile Editor. To the existing payload, add ‘Certificate’ payload and choose the tcp-protector-ca.der file generated in the previous step. DO NOT make any other changes to the profile.
| ⚠️ NOTE - Since the TCP protector certificates come with a validity of 1 year, you may need to rotate the certificate in the configuration file every year with the updated certificate. |
- Save this new profile as GTB_new.mobileconfig file. This profile takes care of - granting Full Disk Access to the GTB Endpoint Agent, preapprove System Extensions, add Web Content Filter and deploy gtbscanner Certificate.
- Deploy this configuration file to the target Mac device(s) using JumpCloud’s Mac MDM Custom Configuration Profile policy.
- On the Mac device, this profile can be seen under Settings > General > Device Management (on macOS 15+) OR Settings > Privacy & Security > Profiles (on macOS 14-) as seen below:
Deploy the GTB Endpoint Agent via JumpCloud Private Repo:
- In the JumpCloud Admin Console, navigate to Software Management and go to the ‘Apple’ section.
- Click on ‘+’ and select JumpCloud Private Repo.
- Upload the .PKG file and name the app ‘GTB Agent’. Once the upload is done, assign the app to target device(s) and click on save.
- Once the app install command is pushed to the endpoint in the backend successfully, app status would reflect ‘Command Sent’ with a Status Code ‘0’.
| ⚠️ NOTE - In general, status code ‘0’ means that JumpCloud has sent the MDM Command to deploy the PKG on the endpoint successfully. This doesn’t necessarily indicate that the installation on the endpoint itself was successful. |
Configure the GTB Endpoint Agent via JumpCloud Commands:
- Finally, you configure the GTB Endpoint on the target Mac device(s) by setting up the CONSOLE IP or HOSTNAME.
- Navigate to JumpCloud Commands, setup a new Command and configure the below script for Mac device(s), set to run as 'root' and Time Out set to '300' seconds:
/Applications/gtb-network-provider.app/Contents/MacOS/gtb-network-provider -i /Library/GTB/support.sh -a CONSOLE IP or HOSTNAME
- Replace the CONSOLE IP or HOSTNAME accordingly, assign the command to the target device(s), save and execute it. Here’s a sample command result of the above Command which informs us that the GTB Endpoint Agent has started:
This step will configure the GTB Agent and set up the Central Console hostname as chosen by you.
At this point, GTB Endpoint Protector Agent should have been successfully installed on the target device(s). Hereafter, for additional information, assistance and technical queries around the Endpoint Agent, you may have to reach out to GTB Support.
Labels:
- Labels:
-
Bash
0 REPLIES 0