New Report Alert - Browser Patch Management Policy Status
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-28-2022 11:19 AM
Hello JC community! I'm here to talk about a new report that we have added to our JumpCloud Reports catalog. This report is named Browser Patch Management Policy report. As you may have already guessed, this report contains data to help admins view all the browser policies that have been deployed to their fleet of devices along with the status for each.
Patch management is one of the premium features within the Jumpcloud platform and it has received a lot of good feedback from many customers leveraging its capabilities. OS Patch Policy Management was released earlier this year. A new report (OS Patch Policy Management report) to support this feature was released shortly after. This report was requested by multiple customers as admins wanted to get a centralized view of all the OS Patch Policies that were deployed on their devices fleet. Last month, the team shipped a new patch feature - Browser Patch Policy (this is available by default to all customers who have access to Patch Management SKU). It was clear to us that we needed another report to go along with this feature and here we are, with this report - Browser Patch Management Policy report. This solves and helps answer the same questions as the OS Patch Management Policy report.
Let’s talk a little about the value this report brings and a scenario when this report can be utilized. More often than not, during a compliance audit, admins are asked to provide evidence about the devices they manage. Being able to provide details about applications like Chrome browsers including policy application, policy status, current version, etc. is key to the audit process. In these cases, such a report that has all the devices listed along with the policy deployed and the status for each of these policies will be tremendously helpful. This ready to use report will save hours for the admins, without which they would have to look at each device individually and create a view for their needs.
Having spoken about what this report is and what value it brings. Let’s now get to the important piece - How to access this report? We have created two access points for this report.
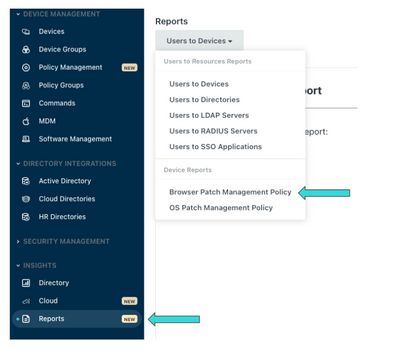
1) Administrators on the JumpCloud platform can access this report just like any other JumpCloud Report in the portfolio. Navigate to the ‘Reports’ tab under the ‘Insights’ section of the left navigation in the Admin Console. On the ‘Reports’ page, there is a dropdown selector that allows Administrators to select the ‘Browser Patch Management Policy’ report under ‘Device Reports’
2) This report can also be accessed on the Patch Management feature page as shown below. This is an easy access point, where the admin can run the report directly from the Browser Patch Policy grid. Navigate to ‘Policy Management’ from the main navigation and click on the ‘Browser’ option under the ‘Patch Management’ tab to see the ‘Run Browser Patch Management Policy Report’ link. Clicking this link would initiate the request to run this report.
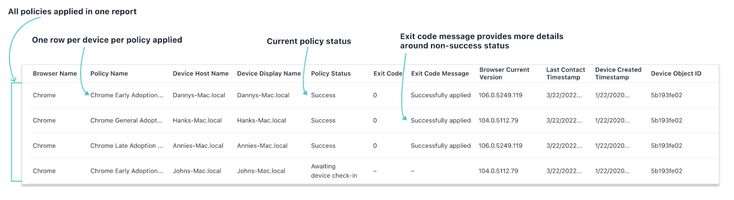
This report includes the browser name, policy name, device host name, device display name, policy status, exit code, exit code messages, current version, last contact timestamp, device created timestamp, and device object id. All of the Browser Patch Management policies available on the JumpCloud platform are included in this report. This feature currently only supports Chrome. As other browser families are added, they will be included in the report. One item of note is that the report will only return devices where a Browser Patch Management policy has been applied. If no Browser Patch Management policies have been applied, the report will return blank.
If you are looking for more information on JumpCloud Reports, check out our JumpCloud Reports knowledge base article and Introducing JumpCloud Reports: It’s More Than Just Data blog post. If you want to learn more about Browser patch management policy, check out How to Not Fall Victim to Browser Vulnerabilities article. Here is another article to get started on how to use the Browser patch management report . Give it a try and let us know what you think.
- Labels:
-
Patch Management