- JumpCloud Community
- IT Topics
- Software & Hardware
- Understanding Upgrading to macOS 13 Ventura
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Understanding Upgrading to macOS 13 Ventura
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-12-2023 10:43 AM
On 22 January 2023, it will mark 90 days since the release of macOS 13 Ventura. This is important because that marks the end of the Major OS Delay period as prescribed by Apple for delaying the rollout of the new major version. Beginning on the 23rd, devices running macOS 12.3 and later will prompt users to install macOS 13 Ventura as a direct upgrade.
Unlike previous years, standard users will be allowed to upgrade to macOS 13 Ventura without admin permission.
Also new this year is a new over-the-air upgrade that is smaller and faster to install, however, it is not driven through a separate application binary which can be watched for and stopped.
These two factors put together mean that the available methods to block the installation of macOS13 Ventura are limited.
This can definitely be an obstacle for organizations that are using software that is not directly compatible with macOS 13 Ventura, and a possible detriment to their working state. We understand that, and we want to help you move safely to macOS 13 Ventura.
If you have not yet, you should update the primary device of one of your trusted colleagues inside your organization – possibly even yourself – to the latest version of macOS. Once you have done that, it’s important to make a list of key software programs that you are running, and key jobs that your staff will have to do to them, and conduct some internal testing.
I chatted with some of our Staff Quality Assurance engineers, and got their feedback on great advice that we could share:
Samuel Harvanek, Lead QA for Team Aluminum (Patch Management), gave us the following items:
“Before I even think about upgrading my own machine, I usually start out testing in a VM! Once I have a VM up (using UTM or Parallels Desktop) and running that version I test the flows and applications critical to my daily workflow. For example, I'll install Docker, Slack, and get our internal environment up and running all within the VM. I test this out until I have that feeling that if I were to upgrade I won't be severely impacted on a day-to-day basis and if anything were to arise it's not something that I couldn't use an extra test machine for! For applications that are harder to test on a VM I like to read the release notes or forums prior to upgrade to see if anyone has experienced issues upgrading.”
Pradnya Deshmukh, Lead QA for Team Tritium (Apple MDM), gave us the following items:
“macOS regression has a pretty wide scope but as part of smoke test I always pick a subset from each area to explore in detail. In terms of how to test or testing prerequisites, starting to test on VM or a test Mac is a good strategy. As Sam pointed out it's possible to revert to previous version if something goes wrong.
In addition, it’s good to work from a list of scenarios you want to check. JumpCloud includes one such list with the Add Devices page for macOS that may help:
It includes policy management, command deployment, software management, patch management, as well as security and operation commands.
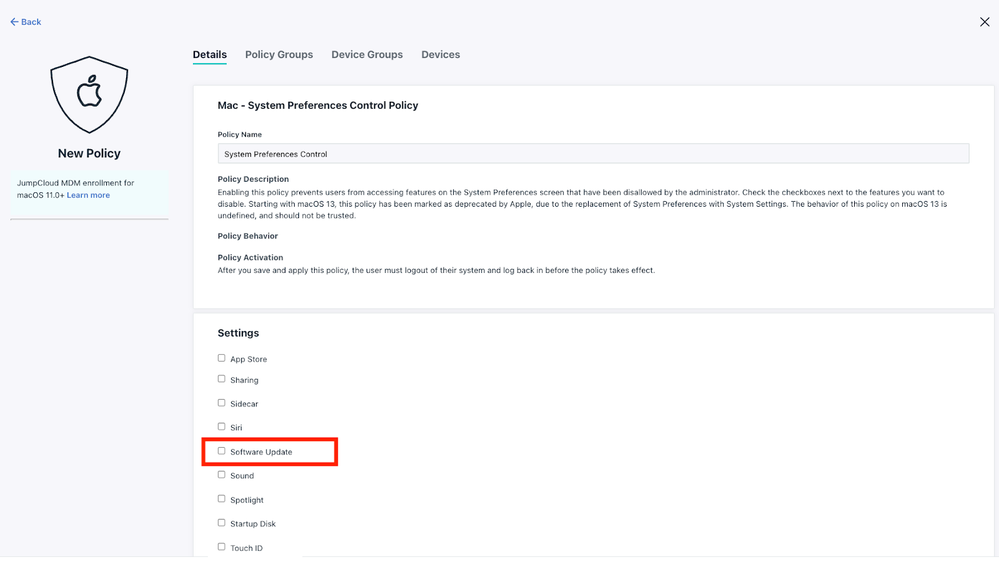
As a last resort, JumpCloud has a policy that will block all software updates for a given set of devices, and that’s the System Preferences Control policy, which can block user access to the Software Update preference pane for proactive prevention of updates.
This will prevent the user from applying any software updates. It should not be used in concert with our Automatic macOS Updates policy, as they will conflict in the user’s experience of the product.
Generally, though, if you’re finding that key software you depend on isn’t updated to keep up with Apple’s own release cycle, you have to consider whether or not it’s serving you well. Being ready on release day, like JumpCloud often is, can be a hard process that not every organization has the ability to do. With Apple saying that they are only fully patching the most recent release of the operating system, and with a maximum delay now of 90 days before updates are freely available to all members of your organization, you need an increased commitment to readiness from your vendor partners.
This can be hard to acquire, but it’s a must for IT Admins in 2023. The costs of ignoring updates are substantial, especially when security is at play. Covering your bases using JumpCloud’s Patch Management product is one way to do that, but it will only help you if your own software is ready for the task.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-13-2023 10:17 AM
Thanks, Tom. Looking forward to having you talk more about this in next week's IT Hour (1.20)
Like someone's post? Give them a kudo!
Did someone's answer help you? Please mark it as a solution.
New to the site? Take a look at these additional resources:
Ready to join us? You can register here.